Comcast still uses MITM javascript injection for messages
For years, Comcast and other large telecommunication companies around the world have injected javascript into your web browsing experience to serve advertisements and account notices. Their ability to do this stems from their upstream position as your Internet Service Provider (ISP). While Comcast is only currently using their javascript injection ability to serve customer account related information, the same message sending vector could be used to serve phishing expeditions, or other types of attacks. Not to mention that whoever your ISP is has access to your browsing history, your search history, your entire internet history unless you use a VPN. Some, like AT&T, even brazenly sold parts of this information for advertising profit unless you explicitly paid them not to – a pay-for-privacy scheme.
A long history of Comcast ads via MITM Javascript injections
The evidence shows that they’ve been doing this since 2014 and earlier. The ISP started to inject code onto the screens of millions of devices connected to Xfinity via free public wireless hotspots. Because they were free, the practice raised both security and net neutrality concerns.
Charlie Douglas, a spokesperson for Comcast, told Ars Technica why there would continue to inject unwanted ads and messages into their users’ web browsers:
“We think it’s a courtesy, and it helps address some concerns that people might not be absolutely sure they’re on a hotspot from Comcast.”
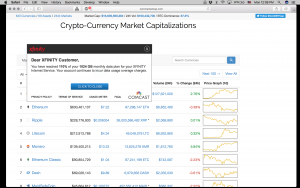
Douglas also reiterated that paying users wouldn’t receive such injected ads or messages at their home. Or at least that was company policy in 2014. Fast forward over two years later, and company policy has clearly changed. Unwanted man-in-the-middle (MITM) code insertion now happens in Xfinity connected homes, as well – a stark reminder that such an attack vector exists. Simply put, this is a centralized vulnerability that could be easily exploited by law enforcement or other nefarious actors.
Source: Privacy Online News
